Free automated penetration testing tools
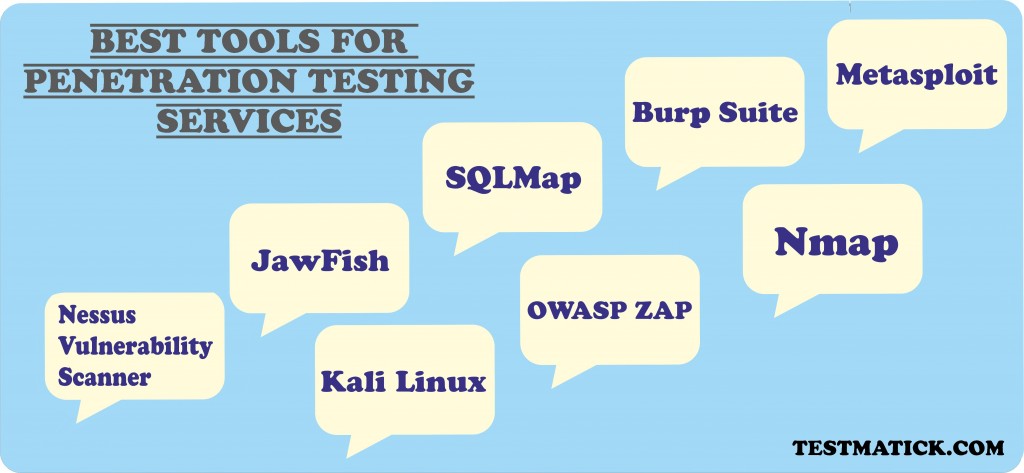
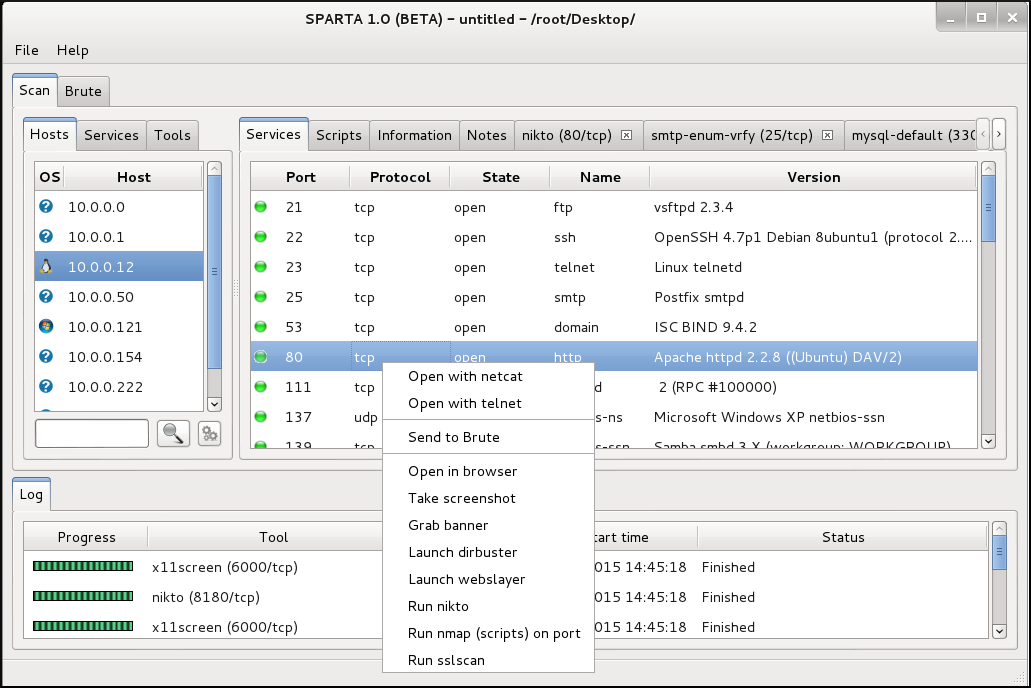
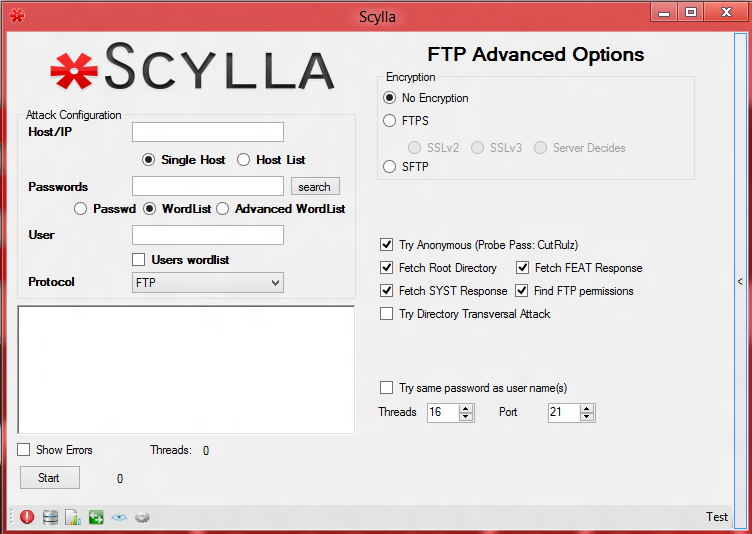
 Penetration testing is the practice of launching authorized, simulated attacks against computer systems and their physical infrastructure to expose potential security weaknesses and vulnerabilities. Wireshark is an industry standard network protocol analysis tool. Use it to save your frequently used scans as profiles, making scanning routines a doddle. If you want to see exactly, some might say microscopically, what's happening on your network then Wireshark is what you need. ZAP is a completely free to use, scanner and security vulnerability finder for web applications. It provides a GUI for well known tools like nmap,hping,tcpdump,volatility,hydra and etc. If we missed any important tool in this list please let us know in the comments below.
Penetration testing is the practice of launching authorized, simulated attacks against computer systems and their physical infrastructure to expose potential security weaknesses and vulnerabilities. Wireshark is an industry standard network protocol analysis tool. Use it to save your frequently used scans as profiles, making scanning routines a doddle. If you want to see exactly, some might say microscopically, what's happening on your network then Wireshark is what you need. ZAP is a completely free to use, scanner and security vulnerability finder for web applications. It provides a GUI for well known tools like nmap,hping,tcpdump,volatility,hydra and etc. If we missed any important tool in this list please let us know in the comments below.




pen test (penetration testing)
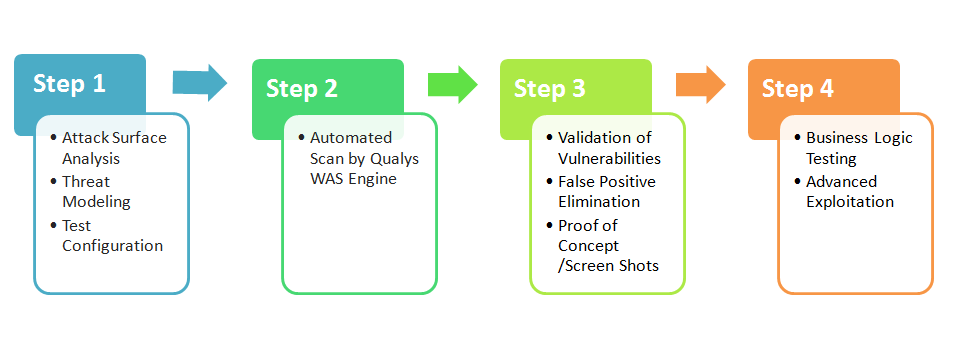
 These distros contain hundreds of other open source tools for network reconnaissance and enumeration, vulnerability scanning, password cracking, wireless security auditing and much more. There are hundreds of advanced penetration methods which can be done either manually or with the help of automation tools. Monitors system response time. Thank you for providing a comprehensive list of pen test tools and making the beginners work easier. This page was last edited on 1 November , at We can figure out the vulnerabilities of a computer system, a web application or a network through penetration testing. So, which site is best for details knowledge about it.
These distros contain hundreds of other open source tools for network reconnaissance and enumeration, vulnerability scanning, password cracking, wireless security auditing and much more. There are hundreds of advanced penetration methods which can be done either manually or with the help of automation tools. Monitors system response time. Thank you for providing a comprehensive list of pen test tools and making the beginners work easier. This page was last edited on 1 November , at We can figure out the vulnerabilities of a computer system, a web application or a network through penetration testing. So, which site is best for details knowledge about it.
37 Powerful Penetration Testing Tools For Every Penetration Tester — Software Testing Help





Penetration Testing: DIY or Hire a Pen Tester?
Description: Once the attacker has exploited one vulnerability they may gain access to other machines so the process repeats i. It is an enterprise-class DDoS protection network Web application firewall helps from the collective intelligence of the entire network Registering domain using CloudFlare is the most secure way to protect from domain hijacking Rate Limiting feature protects user's critical resources. The illegal operation, or payload in Metasploit terminology, can include functions for logging keystrokes, taking screenshots, installing adware , stealing credentials, or altering data. Best of luck bros 20 Alex There are no reporting tools in the list. This site is not just for beginners who are not just enthusiastic but also for experts as a reference.


































User Comments
Post a comment
Comment: